Asa Active Directory Integration
- Asa Active Directory Integration Definition
- Asa Active Directory Integration Tutorial
- Asa Active Directory Authentication Vpn
Connectivity between FMC and Active Directory Firepower module uses TCP port 389 in order to retrieve the User Database from the Active directory. Run packet capture on the Firepower Module to verify connectivity with the Active Directory. ASA(config)# captive-portal interface inside port 1025.
The goal of this article is to quickly show you how you can configure your Firepower Management Center (FMC) to authenticate against Active Directory.
- First login to FMC as a local admin
2. Hover over System, then select Users
3. Select External Authentication
4. Select Add External Authentication Object
5.1 Set the Authentication Method to LDAP, give the object a name (can be anything), set the server type as MS Active Directory
5.2 Set your Primary and Backup AD server (ideally your environment should have two Domain Controllers at a minimum that are on different hardware and disks)
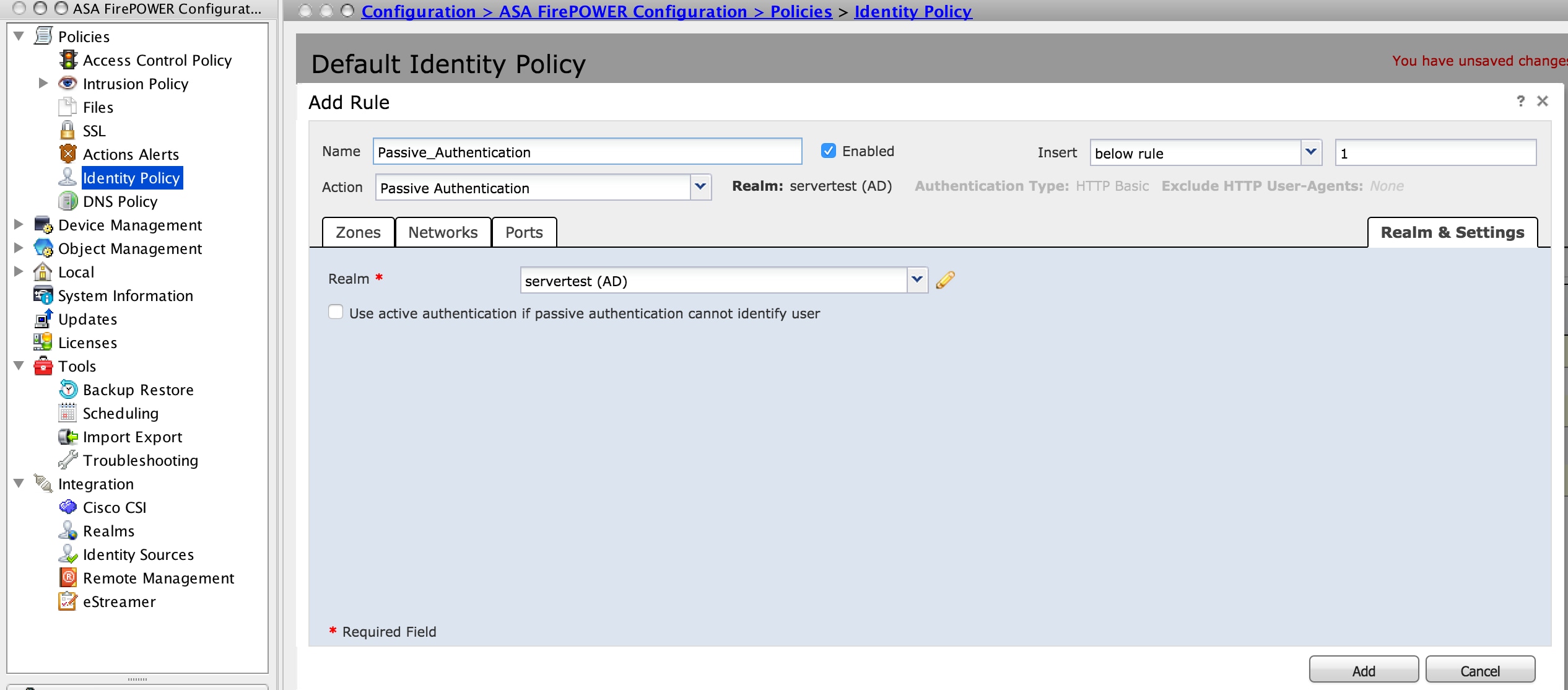
Log in to ASDM, navigate to Configuration ASA FirePOWER Configuration Integration Identity Sources and clickthe User Agent option. After you click on the User Agent option and configure the IP address of User Agent system. Click on Add, as shown in the image: Click on Save button to save the changes. WSA - Active Directory Integration Dear All, I recently deployed S100v appliance in explicit forward mode however I am facing problem while trying to integrate WSA with Active Directory. Cisco ASA – AnyConnect VPN with Active Directory Authentication Complete Setup Guide vektorprime February 18, 2017. This article will discuss setting up Cisco Anyconnect with LDAP/Domain Authentication. I will be showing both the ASDM/GUI and CLI commands.
5.3 Here we will set our base DN for the domain, then an LDAP filter to only allow domain admins. Finally we will finish it off by setting up a Firepower service account in AD (does not need to be an ADMIN, just needs to be able to read objects)
Base DN = dc=domain,dc=local
Base Filter = (memberOf=CN=Domain Admins,CN=Users,dc=domain,dc=local)
Username = CN=fire power,CN=Users,DC=domain,DC=local
Note: In production you should make sure to set up a self signed cert on the DC so that the LDAP session is encrypted. If you were to leave encryption off, a man in the middle attack could grab your AD account and wreck havoc.
5.4 Now we need to set our attribute mapping in FMC. This will be what the the admin types in to login, I chose sAMAccountName for consistency. UPN did not work well for me so I used this.
5.5 The group controlled access roles are if we want to get granular and assign FMC membership of tiers. In my setup I only need domain admins to be able to access FMC as admins, so I did not need to set this up. I left all of these blank, even the default user role.
Asa Active Directory Integration Definition
5.6
The Shell access filter (linux shell) is set to the same as the base filter, you don’t have to do this if you don’t need shell access.
5.6 Go ahead and save this.
5.7 After clicking save it should have taken you one page back into the FMC external authentication page. We now need to save and apply our settings to the FMC.
5.8 Click apply here too
5.9 Now log out and test it!
6 Wohoo that worked!
Head back into the external authentication page where we set all of this up to view your new user profile.
The FMC creates a mapping for every user that logs in externally.
Troubleshooting:
Asa Active Directory Integration Tutorial
The most common problem I foresee with AD authenticated FMC is people mistyping their DN’s so please double check those in section 5.3
Back in the external authentication object, if we edit we can go back in and use the test button.
Scroll all the way to the bottom of the page and input some domain admin credentials to test with.
The page refreshes and we see this:
If we scroll all the way to the bottom we can check the verbose test log.
-->In this tutorial, you'll learn how to integrate Cisco Webex with Azure Active Directory (Azure AD). When you integrate Cisco Webex with Azure AD, you can:
- Control in Azure AD who has access to Cisco Webex.
- Enable your users to be automatically signed-in to Cisco Webex with their Azure AD accounts.
- Manage your accounts in one central location - the Azure portal.
To learn more about SaaS app integration with Azure AD, see What is application access and single sign-on with Azure Active Directory.
Prerequisites
To get started, you need the following items:
- An Azure AD subscription. If you don't have a subscription, you can get a free account.
- Cisco Webex single sign-on (SSO) enabled subscription.
Scenario description
In this tutorial, you configure and test Azure AD SSO in a test environment.
- Cisco Webex supports SP initiated SSO.
- Cisco Webex supports Automated user provisioning.
- Once you configure Cisco Webex you can enforce Session Control, which protect exfiltration and infiltration of your organization’s sensitive data in real-time. Session Control extend from Conditional Access. Learn how to enforce session control with Microsoft Cloud App Security
Adding Cisco Webex from the gallery
To configure the integration of Cisco Webex into Azure AD, you need to add Cisco Webex from the gallery to your list of managed SaaS apps.
- Sign in to the Azure portal using either a work or school account, or a personal Microsoft account.
- On the left navigation pane, select the Azure Active Directory service.
- Navigate to Enterprise Applications and then select All Applications.
- To add new application, select New application.
- In the Add from the gallery section, type Cisco Webex in the search box.
- Select Cisco Webex from results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Configure and test Azure AD single sign-on for Cisco Webex
Configure and test Azure AD SSO with Cisco Webex using a test user called B.Simon. For SSO to work, you need to establish a link relationship between an Azure AD user and the related user in Cisco Webex.
Asa Active Directory Authentication Vpn
To configure and test Azure AD SSO with Cisco Webex, complete the following building blocks:
- Configure Azure AD SSO to enable your users to use this feature.
- Create an Azure AD test user to test Azure AD single sign-on with B.Simon.
- Assign the Azure AD test user to enable B.Simon to use Azure AD single sign-on.
- Configure Cisco Webex to configure the SSO settings on application side.
- Create Cisco Webex test user to have a counterpart of B.Simon in Cisco Webex that is linked to the Azure AD representation of user.
- Test SSO to verify whether the configuration works.
Configure Azure AD SSO
Follow these steps to enable Azure AD SSO in the Azure portal.
In the Azure portal, on the Cisco Webex application integration page, find the Manage section and select Single sign-on.
On the Select a Single sign-on method page, select SAML.
On the Set up Single Sign-On with SAML page, click the edit/pen icon for Basic SAML Configuration to edit the settings.
On the Basic SAML Configuration section, upload the downloaded Service Provider metadata file and configure the application by performing the following steps:
Note
You will get the Service Provider Metadata file from the Configure Cisco Webex section, which is explained later in the tutorial.
a. Click Upload metadata file.
b. Click on folder logo to select the metadata file and click Upload.
c. After successful completion of uploading Service Provider metadata file the Identifier and Reply URL values get auto populated in Basic SAML Configuration section:
A to z bollywood video song hd mp4. In the Sign on URL textbox, paste the value of Reply URL, which gets autofilled by SP metadata file upload.
Photoshop cs5 free download mac crack. Cisco Webex application expects the SAML assertions in a specific format, which requires you to add custom attribute mappings to your SAML token attributes configuration. The following screenshot shows the list of default attributes.
In addition to above, Cisco Webex application expects few more attributes to be passed back in SAML response which are shown below. These attributes are also pre populated but you can review them as per your requirements.
Name Source Attribute uid user.userprincipalname On the Set up Single Sign-On with SAML page, in the SAML Signing Certificate section, find Federation Metadata XML and select Download to download the certificate and save it on your computer.
On the Set up Cisco Webex section, copy the appropriate URL(s) based on your requirement.
Create an Azure AD test user
In this section, you'll create a test user in the Azure portal called B.Simon.
- From the left pane in the Azure portal, select Azure Active Directory, select Users, and then select All users.
- Select New user at the top of the screen.
- In the User properties, follow these steps:
- In the Name field, enter
B.Simon. - In the User name field, enter the username@companydomain.extension. For example,
B.Simon@contoso.com. - Select the Show password check box, and then write down the value that's displayed in the Password box.
- Click Create.
- In the Name field, enter
Assign the Azure AD test user
In this section, you'll enable B.Simon to use Azure single sign-on by granting access to Cisco Webex.
In the Azure portal, select Enterprise Applications, and then select All applications.
In the applications list, select Cisco Webex.
In the app's overview page, find the Manage section and select Users and groups.
Select Add user, then select Users and groups in the Add Assignment dialog.
In the Users and groups dialog, select B.Simon from the Users list, then click the Select button at the bottom of the screen.
In the Add Assignment dialog, click the Assign button.
Configure Cisco Webex
To automate the configuration within Cisco Webex, you need to install My Apps Secure Sign-in browser extension by clicking Install the extension.
After adding extension to the browser, click on Set up Cisco Webex will direct you to the Cisco Webex application. From there, provide the admin credentials to sign into Cisco Webex. The browser extension will automatically configure the application for you and automate steps 3-8.
If you want to setup Cisco Webex manually, sign in to Cisco Cloud Collaboration Management with your full administrator credentials.
Select Settings and under the Authentication section, click Modify.
Select Integrate a 3rd-party identity provider. (Advanced) and go to the next screen.
On the Import Idp Metadata page, either drag and drop the Azure AD metadata file onto the page or use the file browser option to locate and upload the Azure AD metadata file. Then, select Require certificate signed by a certificate authority in Metadata (more secure) and click Next.
Select Test SSO Connection, and when a new browser tab opens, authenticate with Azure AD by signing in.
Return to the Cisco Cloud Collaboration Management browser tab. If the test was successful, select This test was successful. Enable Single Sign-On option and click Next.
Create Cisco Webex test user
In this section, you create a user called B.Simon in Cisco Webex. In this section, you create a user called B.Simon in Cisco Webex.
Go to the Cisco Cloud Collaboration Management with your full administrator credentials.
Click Users and then Manage Users.
In the Manage User window, select Manually add or modify users and click Next.
Select Names and Email address. Then, fill out the textbox as follows:
a. In the First Name textbox, type first name of user like B.
b. In the Last Name textbox, type last name of user like Simon.
c. In the Email address textbox, type email address of user like b.simon@contoso.com.
Click the plus sign to add B.Simon. Then, click Next.
In the Add Services for Users window, click Save and then Finish.
Test SSO
When you select the Cisco Webex tile in the Access Panel, you should be automatically signed in to the Cisco Webex for which you set up SSO. For more information about the Access Panel, see Introduction to the Access Panel.
Additional Resources
